Exemplary Info About How To Prevent Arp Attack
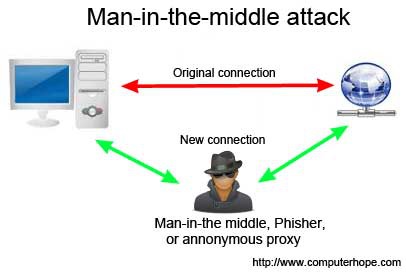
Hackers and unethical attacks on networks provide a continuing threat to take information and cause digital mayhem.
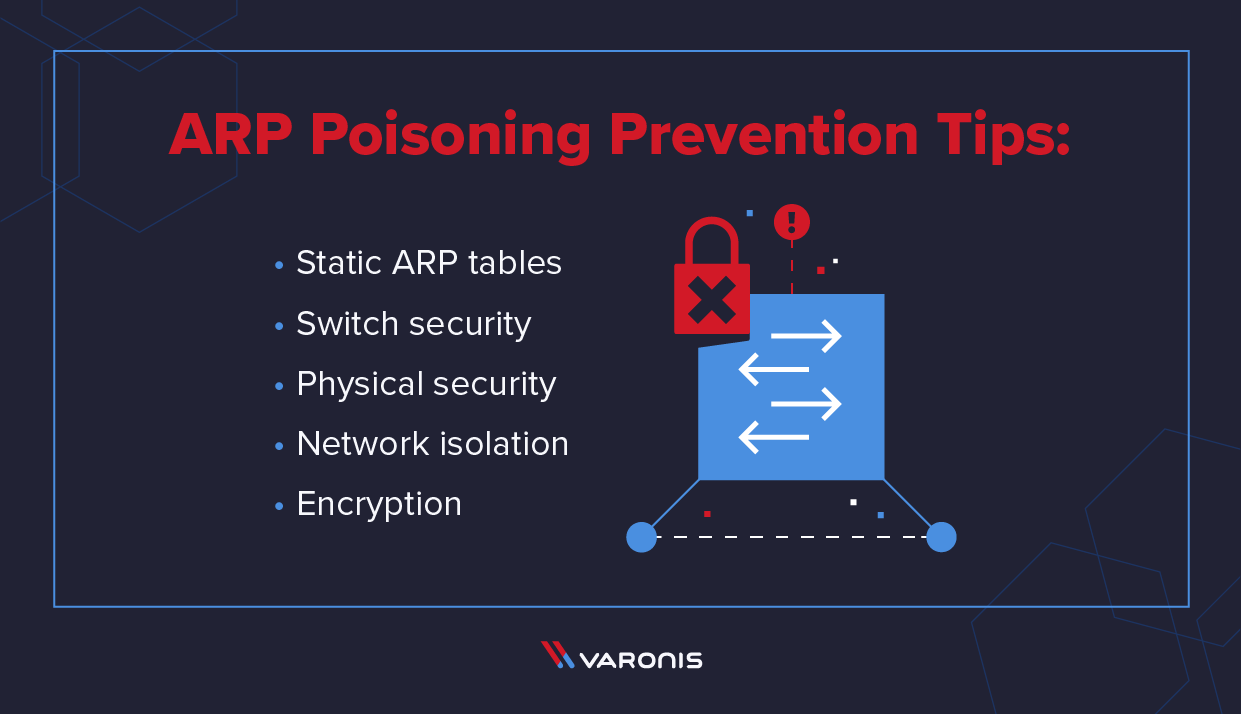
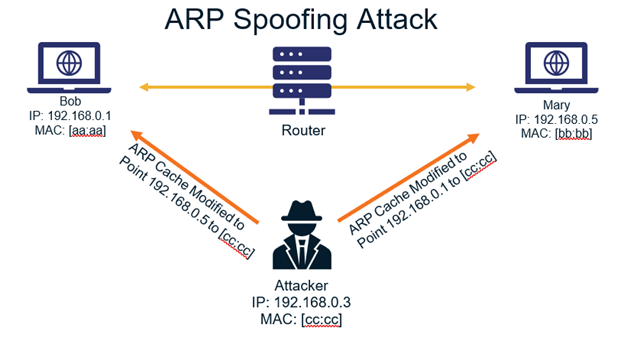
How to prevent arp attack. Arp spoofing detection & prevention authentication & data encoding. So, it will prevent devices from listening on arp responses for that address. How to prevent arp poisoning attacks static arp tables.
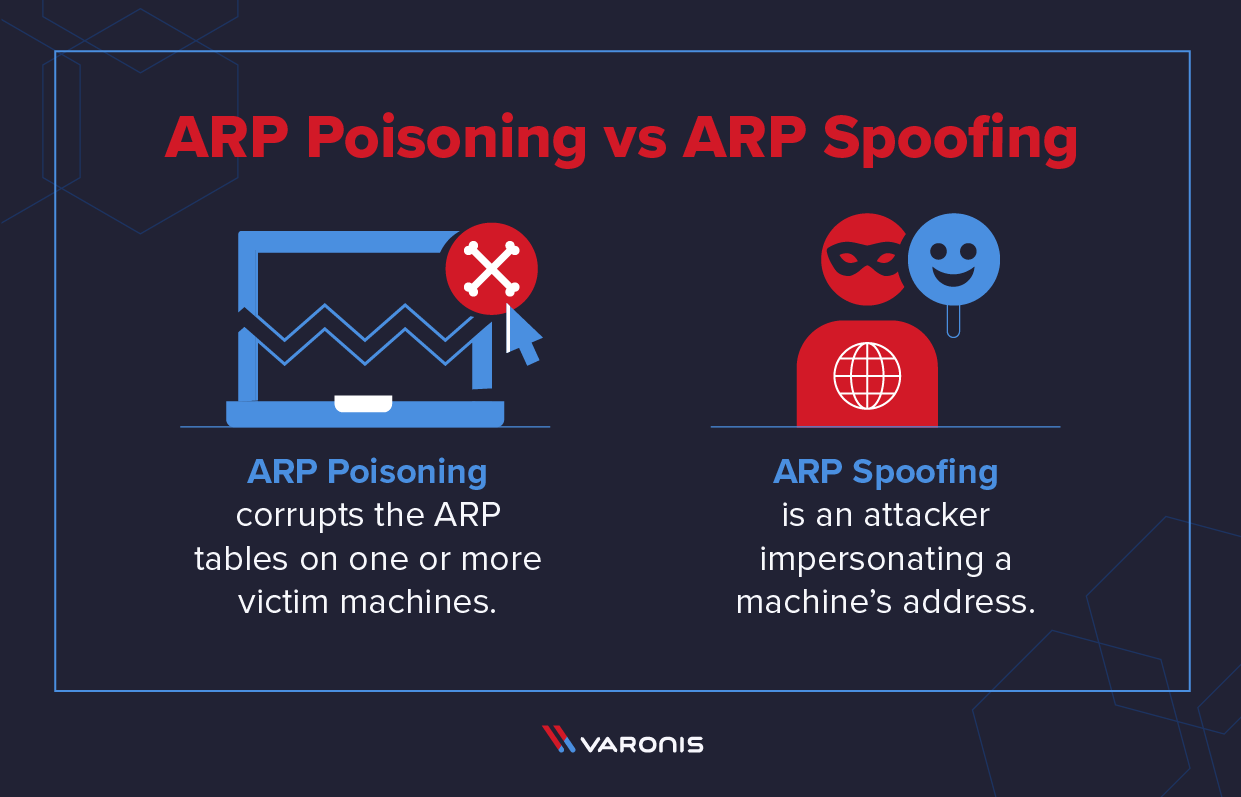
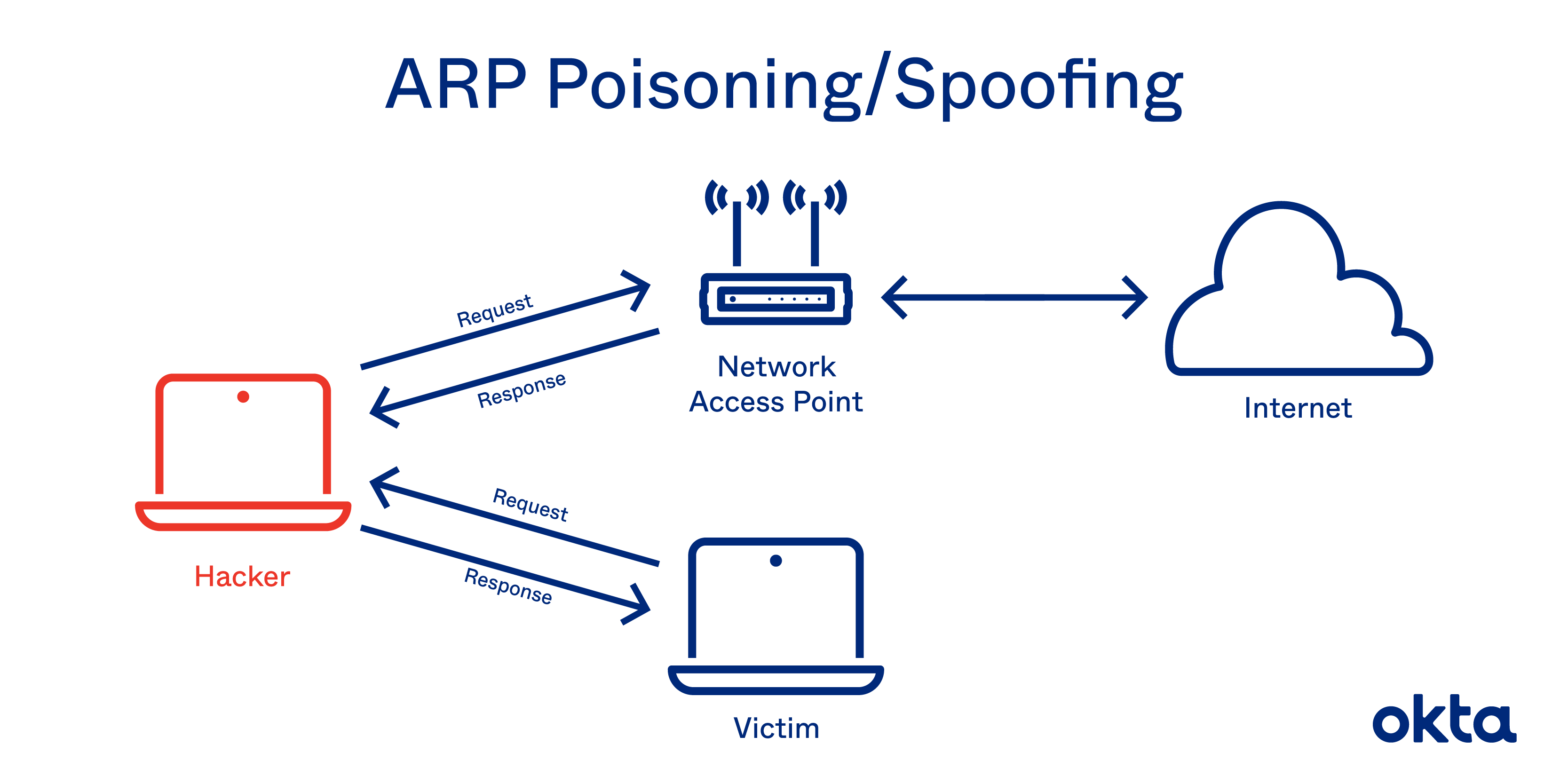
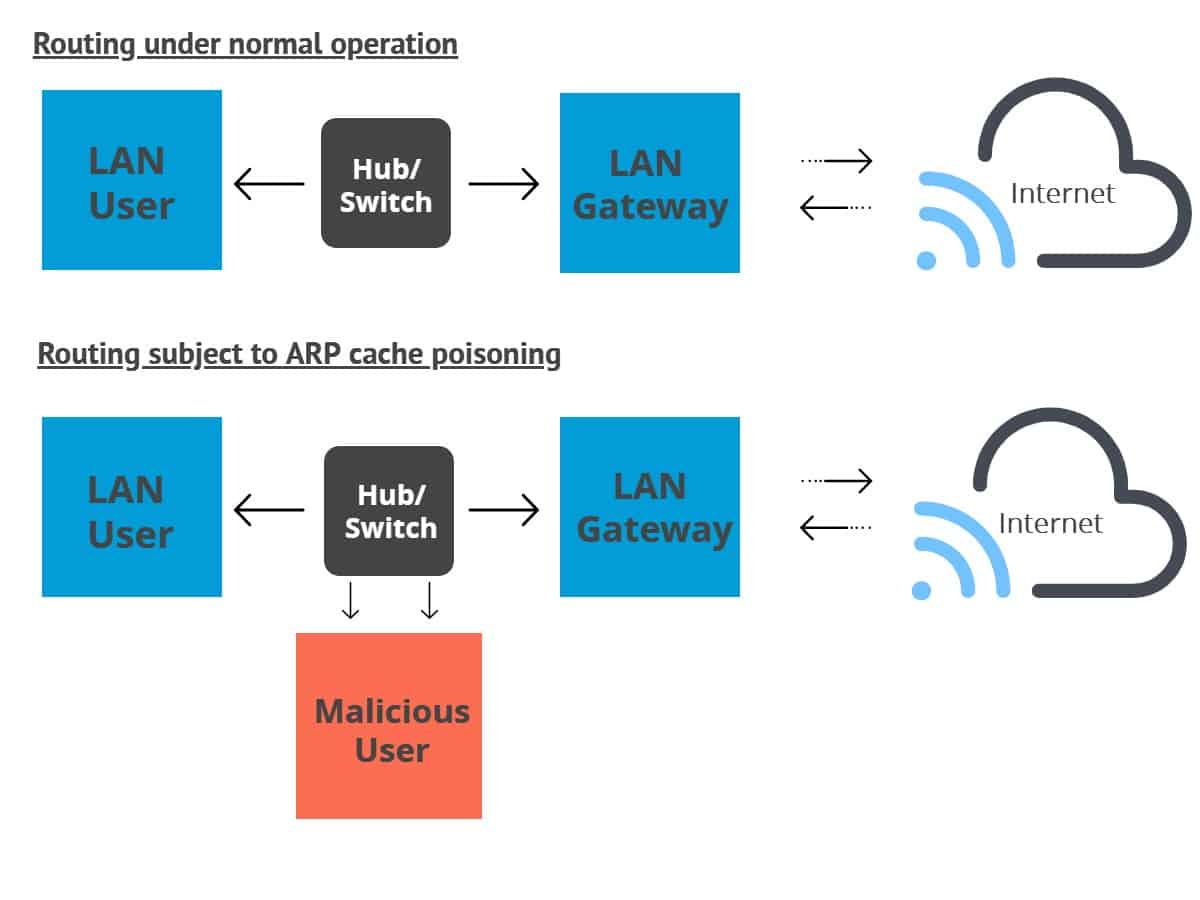
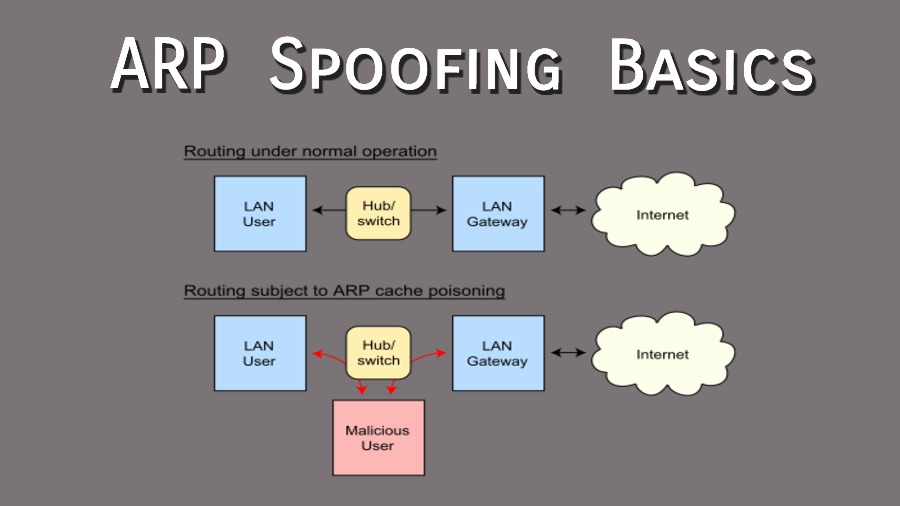
Arp cache poisoning is one of the ways to perform a. Use static arp to allow static entries for. Of course, the two attacks may occur at.
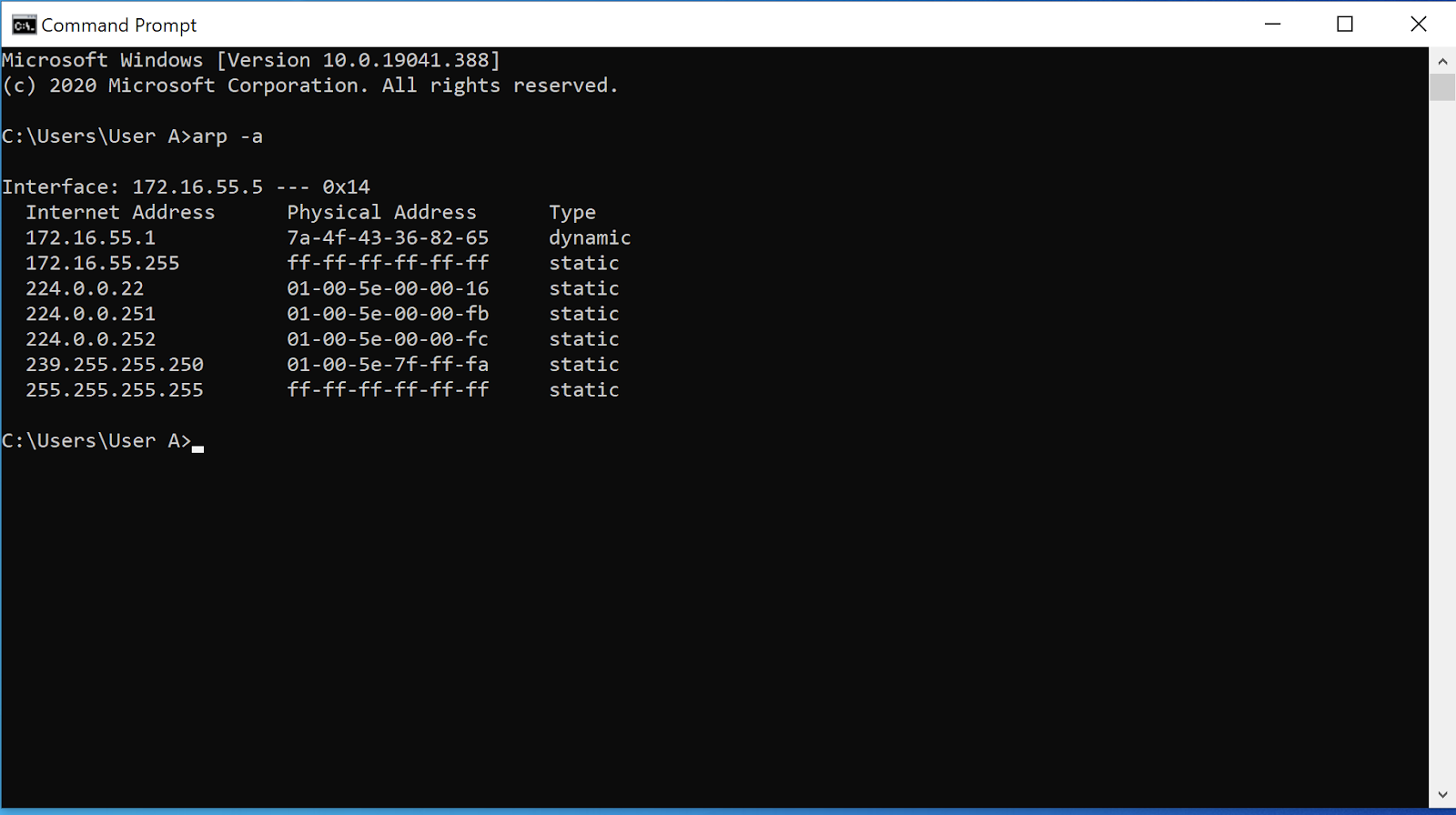
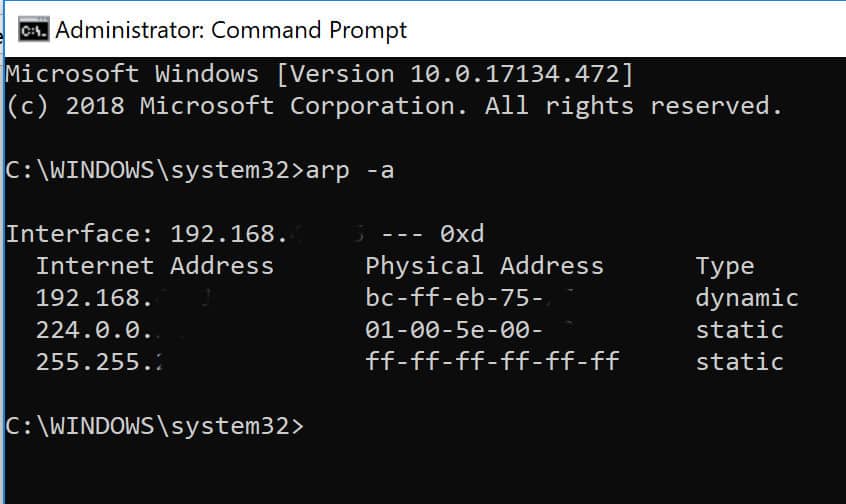
Every bit of sensitive data that you send to your server including your login password, is visible to the attacker. By sending excess arp replies, an attacker can fool a target machine that he can be addressed by the hardware address of another machine in the network. Miscellaneous first, you need to find the ip and mac address of the gateway.
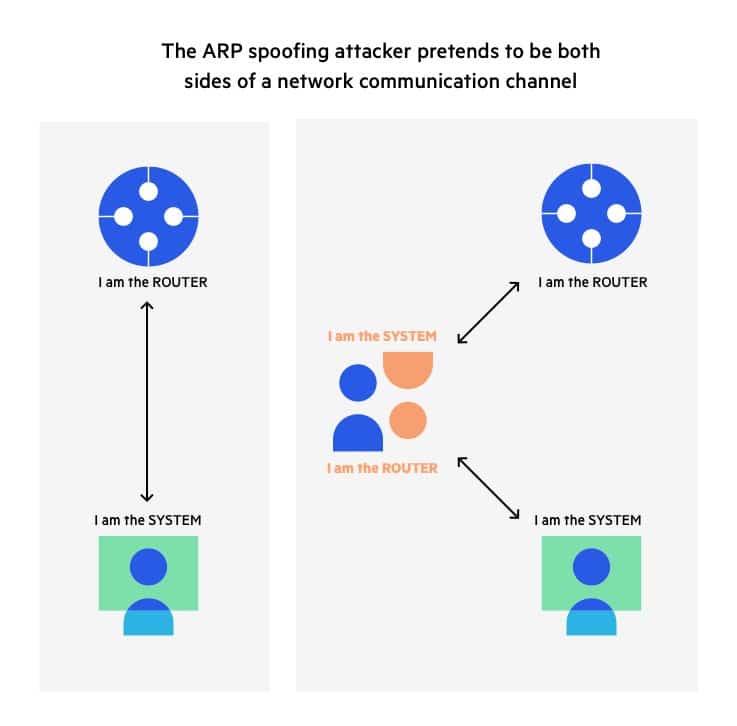
How to set on the router to prevent arp cheat? In the past few months, we’ve seen the term “arp. They send a spoofed arp packet, they send a request that connects to the spoof, and they.
Arp poisoning attack prevention hackers use a predictable series of steps to take over a lan. It is very easy to detect arp attacks (as you may have noticed before with the wireshark screenshot). In the meantime, there are a few things you can do to protect yourself from arp spoofing attacks.
Authenticating a data sender’s identity in some way can prevent receiving data from a. The arp protocol allows you to create a static arp entry for an ip address. Type the username and password in the login page, the default username and password both are admin.
How to prevent arp attacks tags: Let’s discuss the four most effective and commonly used ones. Use static arp entries the risk of.
It’s possible to statically map all the mac addresses in a network to their rightful ip addresses. Use the arp attack protection page to specify how to protect your network against common types of arp attacks and configure the ip&mac binding rules. Firstly, make sure that all devices on your network have unique mac.